
AlmaLinuxに各サーバを立ててCisco機と連携した話(ntp/syslog/radius/snmp)
はじめに
Linuxに下記サーバを立ててCisco機と連携しました。
まずは、IFの設定とSSHの設定を実施。
その後、ntp(chrony)、syslog(rsyslog)、radius(freeradius)、snmp(TWSNMP)のインストール/設定をしました。
おことわり
Linuxはあまり詳しくないので、セキュリティ周りは適当です。
※rootアカウントでのsshログイン許可、SELinuxの停止など
IFの設定
Linuxの設定
nmcli con mod eth0 ipv4.addresses 192.168.11.102/24
nmcli con mod eth0 ipv4.gateway 192.168.11.1
nmcli con mod eth0 +ipv4.dns 8.8.8.8
nmcli con mod eth0 +ipv4.dns 8.8.4.4
nmcli con mod eth0 ipv4.method manual
nmcli con mod eth0 connection.autoconnect yes
nmcli con mod eth0 ipv6.method ignore
nmcli con up eth0※IFの再起動は下記
nmcli con down eth0
nmcli con up eth0
または
nmcli con reloadCisco機の設定
WAN-A-L2-001#show run | section interface GigabitEthernet0/3
interface GigabitEthernet0/3
description To Pnet0
no switchport
ip address 192.168.11.160 255.255.255.0
no ip redirects
no ip proxy-arp
negotiation autoSSH接続
Linuxの設定
rootでログインできるよう変更
※TeraTerm5.0でログインします。古いTeraTermだとログインできないとのこと
cat /etc/ssh/sshd_config
40行目を下記に変更
PermitRootLogin yes
service sshd restartCisco機の設定
user/passとenable passの設定をする。またホスト名、ドメイン名の設定と、ssh version 2の設定、line vtyの設定をする。
※通常はusername xxxx secret や enable secretで暗号化します。
enable password epass
!
username suser password 0 spass
!
hostname WAN-A-L2-001
!
ip domain-name cisco.com
!
ip ssh version 2
!
line vty 0 4
login local
transport input ssh
!crypto key generateをする。
WAN-A-L2-001(config)#crypto key generate rsa
The name for the keys will be: WAN-A-L2-001.cisco.com
Choose the size of the key modulus in the range of 360 to 4096 for your
General Purpose Keys. Choosing a key modulus greater than 512 may take
a few minutes.
How many bits in the modulus [512]: 1024
% Generating 1024 bit RSA keys, keys will be non-exportable...
[OK] (elapsed time was 1 seconds)NTPサーバ
Linuxの設定
chronyのインストール状況の確認
[root@localhost ~]# chronyc -v
chronyc (chrony) version 4.3 (+READLINE +SECHASH +IPV6 +DEBUG)※インストールしていなかったら下記で実行
[root@localhost ~]# dnf -y install chrony参照するNTPサーバの設定
/etc/chrony.conf
3行目を下記に変更
pool ntp.nict.jp iburst
26行目を変更
allow 192.168.0.0/16firewalldに許可追加
[root@localhost ~]# firewall-cmd --add-service=ntp
success
[root@localhost ~]# firewall-cmd --runtime-to-permanent
success動作確認
[root@localhost ~]# chronyc sources
MS Name/IP address Stratum Poll Reach LastRx Last sample
===============================================================================
^* ntp-a2.nict.go.jp 1 6 377 9 -218us[ -273us] +/- 9369us
^- time.cloudflare.com 3 7 377 9 -1964us[-2019us] +/- 67ms
^- x.ns.gin.ntt.net 2 7 377 75 -2926us[-3349us] +/- 79ms
^+ ipv4.ntp3.rbauman.com 2 7 377 74 -808us[-1231us] +/- 8710us"*"がついているので同期できている
参考
Cisco機の設定
設定なし状態での同期状況確認
WAN-A-L2-001#show ntp associations
address ref clock st when poll reach delay offset disp
* sys.peer, # selected, + candidate, - outlyer, x falseticker, ~ configured設定投入
ntp source GigabitEthernet 0/3
ntp server 192.168.11.102 prefer
ntp server 192.168.11.101※sourceはntpサーバにルーティングを追加せず応答可能なIFを設定しました。
また下記を入れるのが推奨されている
service timestamps debug datetime msec localtime show-timezone
service timestamps log datetime msec localtime show-timezone
service sequence-numbers
clock timezone JST 9動作確認したら"~"のみなので設定が入っているだけという状態。
"*"がないので同期はできていない
WAN-A-L2-001#show ntp associations
address ref clock st when poll reach delay offset disp
~192.168.11.101 .INIT. 16 - 256 0 0.000 0.000 15937.
~192.168.11.102 .INIT. 16 - 256 0 0.000 0.000 15937.
* sys.peer, # selected, + candidate, - outlyer, x falseticker, ~ configured強制同期には設定をもう一度入れる
WAN-A-L2-001(config)#ntp server 192.168.11.102 prefer動作確認したら"*"がついているので同期が出来ている
WAN-A-L2-001#show ntp associations
address ref clock st when poll reach delay offset disp
~192.168.11.101 .STEP. 16 - 128 0 0.000 0.000 15937.
*~192.168.11.102 133.243.238.164 2 1 64 1 5.313 -0.135 437.53
* sys.peer, # selected, + candidate, - outlyer, x falseticker, ~ configured※firewallで穴あけしてもPort unreachableが返ってきたので、SELinuxを停止した
vi /etc/selinux/config
28行目を下記に変更
SELINUX=disabled
reboot参考
https://www.infraexpert.com/study/ntpz01.html
syslogサーバ
Cisco機の設定
logging buffered 512000
logging host 192.168.11.102
logging trap informational
logging facility local5Linuxの設定
バージョン確認
[root@localhost ~]# rsyslogd -v
rsyslogd 8.2102.0-117.el9 (aka 2021.02) compiled with:
PLATFORM: x86_64-redhat-linux-gnu
PLATFORM (lsb_release -d):
FEATURE_REGEXP: Yes
GSSAPI Kerberos 5 support: Yes
FEATURE_DEBUG (debug build, slow code): No
32bit Atomic operations supported: Yes
64bit Atomic operations supported: Yes
memory allocator: system default
Runtime Instrumentation (slow code): No
uuid support: Yes
systemd support: Yes
Config file: /etc/rsyslog.conf
PID file: /var/run/rsyslogd.pid
Number of Bits in RainerScript integers: 64動作確認(active(runnning)であることを確認)
[root@localhost ~]# systemctl status rsyslog
● rsyslog.service - System Logging Service
Loaded: loaded (/usr/lib/systemd/system/rsyslog.service; enabled; preset: enabled)
Active: active (running) since Fri 2024-05-03 20:09:06 JST; 32min ago
Docs: man:rsyslogd(8)
https://www.rsyslog.com/doc/
Main PID: 817 (rsyslogd)
Tasks: 3 (limit: 23083)
Memory: 4.5M
CPU: 131ms
CGroup: /system.slice/rsyslog.service
mq817 /usr/sbin/rsyslogd -nfirewallの変更
[root@localhost ~]# firewall-cmd --add-service=syslog
success
[root@localhost ~]# firewall-cmd --runtime-to-permanent
success設定ファイルを編集
※host名ごとにファイルを分ける設計も聞きますが、今回は1つのファイルにまとめます
vi /etc/rsyslog.conf
32行目
module(load="imudp") # needs to be done just once
input(type="imudp" port="514")
一番下
local5.* /var/log/rsyslog/hosts再動
systemctl restart rsyslog 動作確認
[root@localhost rsyslog]# cat /var/log/rsyslog//host.logs
May 18 09:26:15 192.168.11.160 41: 000037: *May 18 09:26:08.916 JST: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet0/3, changed state to up
May 18 09:27:02 192.168.11.160 42: 000038: *May 18 09:26:40.243 JST: %PLATFORM-5-SIGNATURE_VERIFIED: Image 'flash0:/vios_l2-adventerprisek9-m' passed code signing verification
May 18 09:27:03 192.168.11.160 43: 000039: *May 18 09:26:40.244 JST: %LINK-3-UPDOWN: Interface Vlan10, changed state to up
May 18 09:27:03 192.168.11.160 44: 000040: *May 18 09:26:40.245 JST: %LINK-3-UPDOWN: Interface Vlan20, changed state to up
May 18 09:27:03 192.168.11.160 45: 000041: *May 18 09:26:41.244 JST: %LINEPROTO-5-UPDOWN: Line protocol on Interface Vlan10, changed state to up
May 18 09:27:03 192.168.11.160 46: 000042: *May 18 09:26:41.245 JST: %LINEPROTO-5-UPDOWN: Line protocol on Interface Vlan20, changed state to up
May 18 09:39:08 192.168.11.160 47: 000043: *May 18 09:39:06.982 JST: %SYS-5-CONFIG_I: Configured from console by console
May 18 09:40:31 192.168.11.160 48: 000044: *May 18 09:40:29.288 JST: %SYS-5-CONFIG_I: Configured from console by console
May 18 09:50:13 192.168.11.160 49: 000045: May 18 09:50:12.393 JST: %SYS-5-CONFIG_I: Configured from console by suser on vty0 (192.168.11.13)
May 18 09:51:51 192.168.11.160 50: 000046: May 18 09:51:51.096 JST: %SYS-5-CONFIG_I: Configured from console by console
[root@localhost ~]#参考
https://qiita.com/sugar_salt75/items/1d1980d5b66becc9f38f
https://www.infraexpert.com/study/syslog2.html
Radiusサーバ
Linuxの設定
下記でインストール
#dnf install freeradius freeradius-utilsバージョン確認
[root@localhost ~]# radiusd -v
radiusd: FreeRADIUS Version 3.0.21, for host x86_64-redhat-linux-gnu
FreeRADIUS Version 3.0.21
(略)radiusd.confの337行目あたりで認証ログを残すようにする。
※必要に応じてでOK
[root@localhost ~]# vi /etc/raddb/radiusd.conf
auth = yes
auth_badpass = yes
auth_goodpass = yesclients.confの250行目あたりで、認証対象のセグメントを指定。
※0.0.0.0/0で全セグメントを指定することも可能
[root@localhost ~]# vi /etc/raddb/clients.conf
client private-network-1 {
ipaddr = 192.168.11.0/24
secret = cisco-secret
}
client private-network-2 {
ipaddr = 172.0.0.0/8
secret = cisco-secret
}
client private-network-3 {
ipaddr = 10.0.0.0/8
secret = cisco-secret
}usersにuser名とpasswordを記載
[root@localhost ~]# vi /etc/raddb/users
ruser Clieartext-Password := "rpass"証明書関係の操作
cd /etc/raddb/certs
make all
chmod 755 server.pem dhenableで起動時有効にしつつ、radiusdを起動する。
systemctl enable radiusd
systemctl start radiusdfirewalldに許可追加
[root@localhost ~]# firewall-cmd --add-service=radius
success
[root@localhost ~]# firewall-cmd --runtime-to-permanent
successCisco機の設定
aaa new-model
aaa session-id common
aaa authentication login default group radius local
ip radius source-interface Loopback 0
radius server RadiusServer#1
address ipv4 192.168.11.102 auth-port 1812 acct-port 1813
key cisco-secret動作確認
[root@localhost certs]# cat /var/log/radius/radius.log
Sat May 18 10:55:33 2024 : Info: Debugger not attached
Sat May 18 10:55:33 2024 : Warning: tls: Please use 'tls_min_version' and 'tls_max_version' instead of 'disable_tlsv1'
Sat May 18 10:55:33 2024 : Warning: tls: Please use 'tls_min_version' and 'tls_max_version' instead of 'disable_tlsv1_1'
Sat May 18 10:55:33 2024 : Warning: tls: Setting DH parameters from /etc/raddb/certs/dh - this is no longer necessary.
Sat May 18 10:55:33 2024 : Warning: tls: You should comment out the 'dh_file' configuration item.
Sat May 18 10:55:33 2024 : Info: Loaded virtual server <default>
Sat May 18 10:55:33 2024 : Warning: Ignoring "sql" (see raddb/mods-available/README.rst)
Sat May 18 10:55:33 2024 : Warning: Ignoring "ldap" (see raddb/mods-available/README.rst)
Sat May 18 10:55:33 2024 : Info: Loaded virtual server default
Sat May 18 10:55:33 2024 : Info: # Skipping contents of 'if' as it is always 'false' -- /etc/raddb/sites-enabled/inner-tunnel:336
Sat May 18 10:55:33 2024 : Info: Loaded virtual server inner-tunnel
Sat May 18 10:55:33 2024 : Info: Debugger not attached
Sat May 18 10:55:33 2024 : Warning: tls: Please use 'tls_min_version' and 'tls_max_version' instead of 'disable_tlsv1'
Sat May 18 10:55:33 2024 : Warning: tls: Please use 'tls_min_version' and 'tls_max_version' instead of 'disable_tlsv1_1'
Sat May 18 10:55:33 2024 : Warning: tls: Setting DH parameters from /etc/raddb/certs/dh - this is no longer necessary.
Sat May 18 10:55:33 2024 : Warning: tls: You should comment out the 'dh_file' configuration item.
Sat May 18 10:55:33 2024 : Info: Loaded virtual server <default>
Sat May 18 10:55:33 2024 : Warning: Ignoring "sql" (see raddb/mods-available/README.rst)
Sat May 18 10:55:33 2024 : Warning: Ignoring "ldap" (see raddb/mods-available/README.rst)
Sat May 18 10:55:33 2024 : Info: Loaded virtual server default
Sat May 18 10:55:33 2024 : Info: # Skipping contents of 'if' as it is always 'false' -- /etc/raddb/sites-enabled/inner-tunnel:336
Sat May 18 10:55:33 2024 : Info: Loaded virtual server inner-tunnel
Sat May 18 10:55:33 2024 : Info: Ready to process requests
Sat May 18 10:56:17 2024 : Auth: (0) Login OK: [ruser/rpass] (from client private-network-1 port 3)
Sat May 18 10:57:27 2024 : Auth: (1) Login OK: [ruser/rpass] (from client private-network-1 port 3)SNMPサーバ
Cisco機の設定
snmp-server community cisco-community RO 1
snmp-server trap-source Loopback0
snmp-server enable traps snmp authentication linkdown linkup coldstart warmstart
snmp-server host 192.168.11.102 version 2c cisco-community
snmp ifmib ifindex persistLinuxの設定
TWSNMP FC版を使用します。
AlmaLinux版(RHEL版?)はなさそうだったのでdockerを使います。
※TWSNMPの公式サイトはこちら
レポジトリを更新し、インストールと起動を実施
#sudo dnf config-manager --add-repo=https://download.docker.com/linux/centos/docker-ce.repo
Adding repo from: https://download.docker.com/linux/centos/docker-ce.repo
# dnf repolist | grep docker
docker-ce-stable Docker CE Stable - x86_64
#sudo dnf install docker-ce docker-ce-cli containerd.io docker-buildx-plugin docker-compose-plugin
#sudo systemctl start dockerhello worldで動作確認
# sudo docker run hello-world
Unable to find image 'hello-world:latest' locally
latest: Pulling from library/hello-world
c1ec31eb5944: Pull complete
Digest: sha256:266b191e926f65542fa8daaec01a192c4d292bff79426f47300a046e1bc576fd
Status: Downloaded newer image for hello-world:latest
Hello from Docker!
This message shows that your installation appears to be working correctly.
To generate this message, Docker took the following steps:
1. The Docker client contacted the Docker daemon.
2. The Docker daemon pulled the "hello-world" image from the Docker Hub.
(amd64)
3. The Docker daemon created a new container from that image which runs the
executable that produces the output you are currently reading.
4. The Docker daemon streamed that output to the Docker client, which sent it
to your terminal.
To try something more ambitious, you can run an Ubuntu container with:
$ docker run -it ubuntu bash
Share images, automate workflows, and more with a free Docker ID:
https://hub.docker.com/
For more examples and ideas, visit:
https://docs.docker.com/get-started/TWSNMP FCを起動
docker volume create twsnmpfc
docker run --rm -d --net host -v twsnmpfc:/datastore twsnmp/twsnmpfcブラウザでアクセス(AlmalinuxのIPでOK)
URLは「http://192.168.11.102:8080/」と8080ポートを使用します。

user:twsnmp
pass:twsnmp
でログイン

左のメニュ→システム設定→マップ→Community名を変更する。またSNMP TRAPをONにする(画像は変更前)
今回はCisco機の設定にあわせて「cisco-community」とする。

変更後の画像

firewalldに許可追加
[root@localhost ~]# firewall-cmd --add-service=snmp
success
[root@localhost ~]# firewall-cmd --add-service=snmptrap
success
[root@localhost ~]# firewall-cmd --runtime-to-permanent
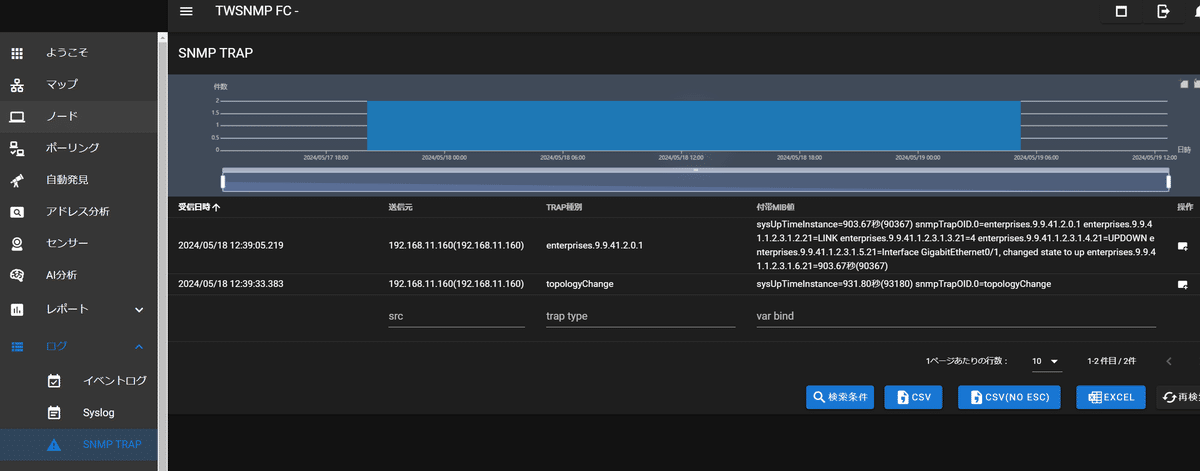
successtrapを受信できている
MAPの作り方などは、参考サイト参照。
参考
この記事が気に入ったらサポートをしてみませんか?
